
What a Virtual CISO Actually Costs (And How to Tell If You're Getting Value)
How much does a virtual CISO cost? Typically $3,500 to $15,000 per month. Engagement models, what drives price up or down, and how to evaluate value.
10 articles in this category

How much does a virtual CISO cost? Typically $3,500 to $15,000 per month. Engagement models, what drives price up or down, and how to evaluate value.
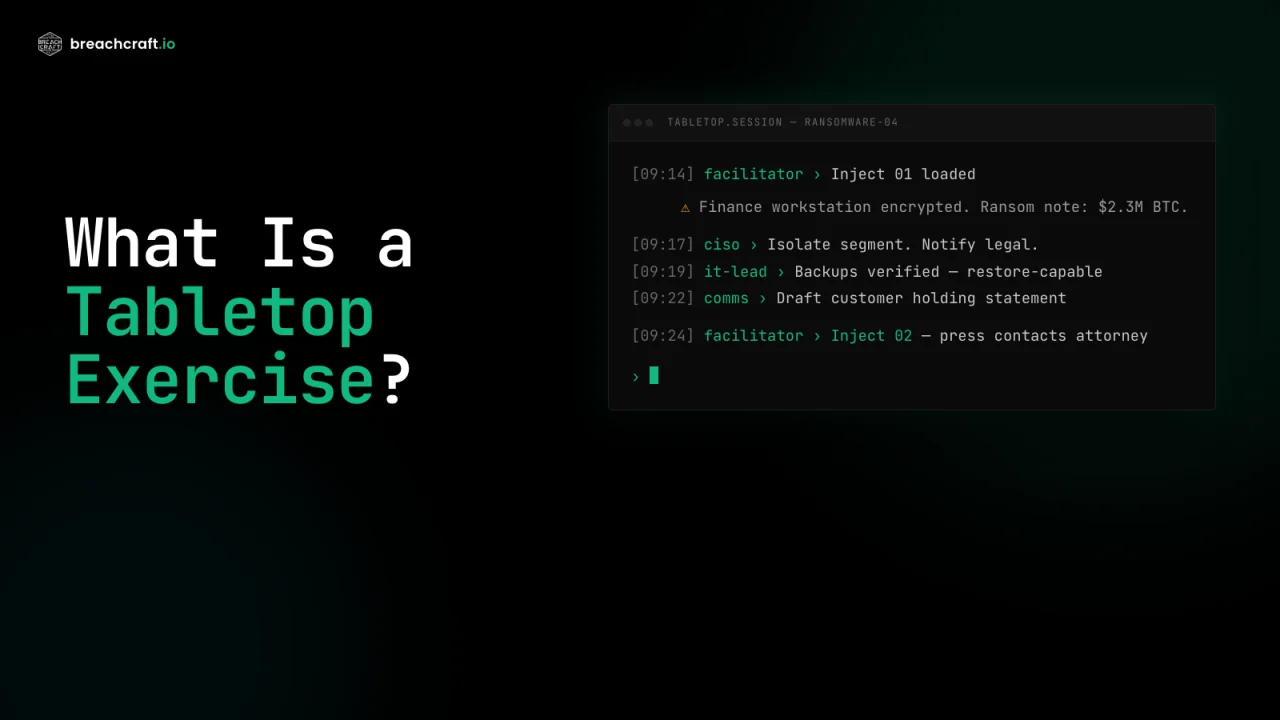
A tabletop exercise stress-tests your incident response plan without real consequences. Learn how they work, who attends, what you get, how often to run.

Vulnerability assessments find known issues. Penetration tests prove what an attacker can actually do. Here's how to decide which one your organization needs.

A structured framework for assessing security risks associated with artificial intelligence systems, covering OWASP LLM Top 10 and NIST AI RMF.

Learn how wireless penetration testing evaluates your wireless infrastructure security using the same techniques employed by malicious attackers.

Learn how Virtual CISO services provide experienced security leadership on a fractional basis, helping organizations build mature security programs without the cost of a full-time executive.

Learn what web application penetration testing is, why your organization needs it, and what to expect from a thorough security assessment.

Learn how gap assessments compare your current security practices against established frameworks like NIST, CIS, and ISO 27001 to identify improvement opportunities.

Learn what penetration testing is, why your organization needs it, how to choose the right provider, and what to expect from the assessment process.
Learn how CIS Controls v8 gap assessments help organizations evaluate and systematically improve their cybersecurity posture through Implementation Groups.