What is a Tabletop Exercise? A Complete Guide
A tabletop exercise stress-tests your incident response plan without real consequences. Learn how they work, who attends, what you get, how often to run.
It’s 3 AM. Your phone buzzes with an alert: ransomware has been detected on your network. Customer data may be at risk. Your CEO wants answers. Legal wants to know your notification obligations. IT is trying to figure out what’s actually encrypted and what’s recoverable from backups.
Is that really how you want to discover the gaps in your incident response plan?
A tabletop exercise is how you find those gaps before the alert comes in. This guide covers what tabletops are, what they actually test, who needs to be in the room, and what separates a useful exercise from two wasted hours on a conference call.
What Is a Tabletop Exercise?
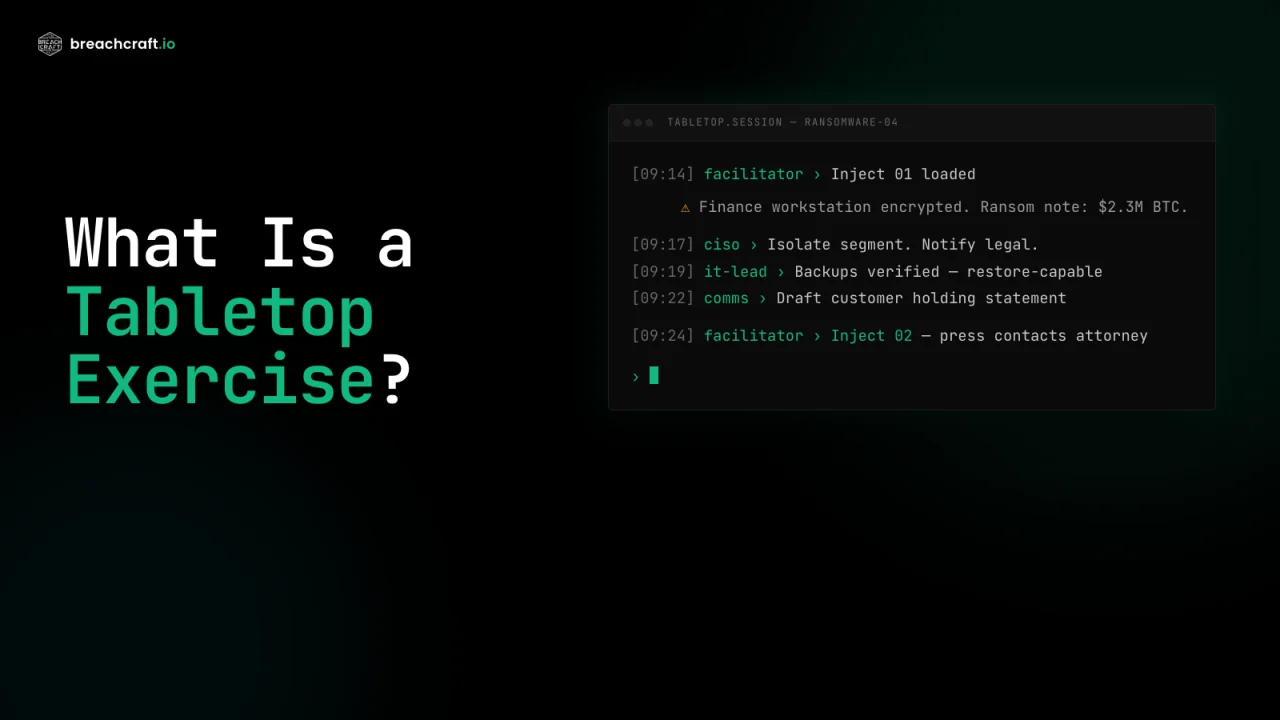
A tabletop exercise is a facilitated discussion that walks your team through a simulated security incident. Participants respond to an unfolding scenario in real time, making decisions, coordinating across teams, and surfacing gaps in your incident response plan. Unlike a penetration test, a tabletop tests people and processes, not technology. No systems are affected. Nothing goes offline.
The goal is to expose weaknesses (missing playbooks, unclear ownership, broken communication chains, untested decisions) before a real incident forces you to find them the hard way.
Why They Matter
Most mature security programs run tabletops for two reasons: compliance and readiness. The compliance case is easy to document. The readiness case is harder to quantify but much more valuable.
Compliance Frameworks Expect IR Testing
| Framework | Requirement |
|---|---|
| NIST SP 800-53 (Rev. 5) | IR-3: Incident Response Testing, at least annually |
| NIST CSF 2.0 | RS.MA and ID.IM: test and improve response capability |
| PCI DSS 4.0 | Req. 12.10.2: test incident response plan at least annually |
| HIPAA Security Rule | 164.308(a)(6): response and reporting procedures documented and tested |
| SOC 2 | CC7.4: incident response procedures evaluated for effectiveness |
| ISO/IEC 27001:2022 | A.5.24 and A.5.25: IR planning, assessment, and decision-making |
| CMMC 2.0 Level 2 | IR.L2-3.6.3: test IR capability |
| FedRAMP | IR-3: annual incident response testing |
Tabletops are the most efficient way to satisfy these. They produce documented evidence (attendance records, after-action report, remediation tracking) without the cost of a live exercise or full-scale simulation. For detail on the NIST requirement, see NIST SP 800-61 Rev. 2, the official computer security incident handling guide.
Readiness Beats Compliance
The real reason to run a tabletop is that incidents compress time. Decisions that feel straightforward in a planning meeting become agonizing when the CEO is on the line, a customer is on Twitter, and the ransom deadline is in four hours. Teams that have practiced under pressure make those decisions faster. Teams that haven’t freeze.
A recent engagement illustrated the point. A mid-market insurance carrier ran their annual ransomware tabletop with us and the exercise surfaced three specific IR plan gaps nobody had noticed — disabled threat-hunting telemetry in their existing tooling, an escalation plan that assumed the primary comms channel would still work, and single-person knowledge silos on critical platforms. Read the full engagement: Three Gaps an Annual Ransomware Tabletop Exposed.
How a Tabletop Is Structured
A well-run tabletop has three parts.
1. Pre-Exercise
Scenario design, participant list, ground rules. This is where most of the value is decided. A facilitator who knows your industry and tech stack can build a scenario that actually stresses your program. One who doesn’t will run a generic script.
2. The Exercise
The scenario unfolds in timed phases. The facilitator introduces injects (new information or complications) that force decisions. An inject might be:
- “Your disaster recovery site is also showing signs of compromise.”
- “A customer just posted screenshots of the outage on LinkedIn.”
- “The attacker has moved the ransom deadline up by six hours.”
- “Your primary legal counsel is on vacation and unreachable.”
Participants talk through how they’d respond. The facilitator captures decisions, pauses when coordination breaks down, and keeps the exercise moving without letting it become performative.
3. Hot Wash and After-Action Report
The hot wash is the immediate debrief, usually 30 to 45 minutes right after the exercise ends. Memory is fresh. Honest observations come out. A few days later, the after-action report formalizes those observations with specific findings, framework mapping, and prioritized recommendations.
If you don’t get a written after-action report with assigned owners and timelines, you didn’t get a tabletop. You got a discussion.
Common Scenario Types
Any of these can be scoped into a half-day exercise. A full-day exercise often combines two or chains them (ransomware that pivots into a data breach, or a supply chain compromise that becomes an insider investigation).
Ransomware
The most common starter. Tests containment decisions, backup viability, payment authority, regulatory notification, and customer communication. A good ransomware exercise reveals that backups haven’t been tested in production, network segmentation doesn’t work the way the diagram says, and nobody knows who can authorize a ransom payment.
Business Email Compromise
Finance-focused. A fraudulent wire request from an impersonated executive. Tests verification procedures, out-of-band confirmation, bank fraud recall, and the organizational pressure that makes BEC attacks succeed. Exercises here almost always surface a policy that says “verify with a phone call” and a finance team that verifies by replying to the email. BEC is one of the FBI IC3’s top-reported crimes by dollar loss, so the muscle memory matters.
Data Breach Discovery
Legal-heavy. Evidence suggests customer data was exfiltrated. Tests forensic coordination, notification timelines (GDPR’s 72 hours, state breach laws, HIPAA’s 60 days), and the question of when to loop in outside counsel. Having your actual legal counsel in the room changes this scenario entirely.
Insider Threat
HR-coordinated. A privileged employee shows signs of malicious or negligent activity. Tests the investigation process, evidence handling, access revocation timing, and the coordination between security, HR, and legal that has to happen before confrontation.
Supply Chain Compromise
Vendor-coordinated. A trusted software provider announces a compromise affecting your installation. Tests vendor communication, impact assessment when the attacker had legitimate access, isolation decisions, and downstream notification if you’re a vendor yourself. See CISA’s guidance on ICT supply chain risk management for context on how federal agencies frame the threat.
Major Service Outage
Business continuity focused. Primary systems offline, customers affected, recovery prioritization under pressure. Good for teams that have never operated under a hard time constraint.
Who Should Be in the Room
Not just IT. This is the single biggest mistake organizations make.
A real incident pulls in:
- IT security and IT operations to investigate and contain
- Legal for notification decisions and privilege
- Communications or PR for customer and media response
- HR for insider scenarios or employee-impacting decisions
- Executive leadership for the decisions that require CEO or CFO authority
- Business unit owners for the systems and data they’re responsible for
- External counsel or IR firm if pre-arranged retainers exist
If those people aren’t in the tabletop, you’re not practicing the response you’ll actually execute. You’re practicing IT’s slice of it.
For critical vendor dependencies (a managed security provider, an IR retainer, a cloud host), advanced programs invite those vendors to participate in the exercise. It exposes coordination gaps in both directions.
What a Good Facilitator Does Differently
The facilitator sets the ceiling on the exercise. A strong one builds pressure without breaking trust. A weak one reads from a script and lets the room talk itself into a clean answer that wouldn’t survive a real incident.
Signs you have a strong facilitator:
- The scenario reflects your industry, tech stack, and known threats (not a template)
- Injects force decisions rather than inviting discussion
- Teams get called on when they drift into hypothetical best-case answers
- The facilitator has actually led incident response in real breaches
- The after-action report names specific moments and decisions, not generalities
- Recommendations have owners and timelines, not “improve communication”
Signs you hired the wrong provider:
- Generic scenario that could apply to any organization
- No pushback when the room glosses over a hard decision
- After-action report that reads like it could have been written without running the exercise
- Recommendations that say “develop incident response capability” (you already have one, and that’s why you’re running this)
Common Mistakes
- IT-only invitations. You’ll learn about IT’s response. Everything else will be discovered during a real incident.
- Same scenario every year. Ransomware is a good starter. By the third annual ransomware tabletop, you’re rehearsing the same muscles. Rotate.
- No follow-through. The after-action report lands, gets forwarded to the team, and nothing happens. Recommendations need owners, due dates, and quarterly check-ins.
- Treating it as a performance. If people are worried about looking bad, they’ll give you the textbook answer instead of the honest one. Psychological safety isn’t optional.
- Buying a facilitator who’s never responded to a real incident. They don’t know where to push.
What You Get Out of It
A professionally run tabletop produces:
- An after-action report with specific findings tied to moments in the exercise
- A gap analysis mapping findings to your controls framework (CIS Top 18 and NIST 800-53 on our engagements)
- Prioritized recommendations with owners and timelines
- Positive observations documenting what worked, which matters for both morale and audit evidence
- Compliance documentation sufficient to satisfy NIST, PCI, SOC 2, ISO, and CMMC testing requirements
- Optional playbook updates if you want the provider to revise your IR plan based on what the exercise revealed
How Often to Run Them
- Annually at minimum. Most frameworks require this and most programs default to it.
- Semi-annually if you’re in a heavily regulated industry, growing fast, or have had recent turnover.
- Trigger events. Run an exercise after major technology changes (cloud migration, M&A, new core system), after a real incident (test the updated plan), or before a compliance audit that will look for evidence of IR testing.
The cost of running an extra exercise is low. The cost of finding a gap during a real incident is high.
How to Choose a Provider
When evaluating a tabletop provider, ask:
- Have you personally led incident response in actual breaches?
- Can I see a sample after-action report (redacted)?
- How do you tailor scenarios to my industry and tech stack?
- Are executives and non-IT participants handled as well as technical staff?
- What framework do you map findings to?
- Do your deliverables satisfy [specific compliance framework] audit evidence?
If you can’t get clean answers to those, keep looking.
Cost Context
Most organizations budget $5,000 to $20,000 for a professionally facilitated tabletop. The range depends on scenario complexity, number and seniority of participants, whether external stakeholders (legal counsel, key vendors) are included, and whether deliverables extend beyond the after-action report into playbook updates or policy revisions.
Compared to the cost of a single incident, that’s inexpensive insurance. Compared to the cost of a single compliance finding, it’s a rounding error.
The Bottom Line
Tabletops are cheap, high-value, and required by almost every framework your organization cares about. They’re also the closest thing you’ll get to practicing an incident without having one. Skip them and you’re betting that your first real incident won’t reveal anything your plan didn’t already account for. That’s not a bet worth taking.
Ready to test your incident response plan? Contact Breach Craft to discuss a tabletop exercise tailored to your organization, technology stack, and risk profile.


